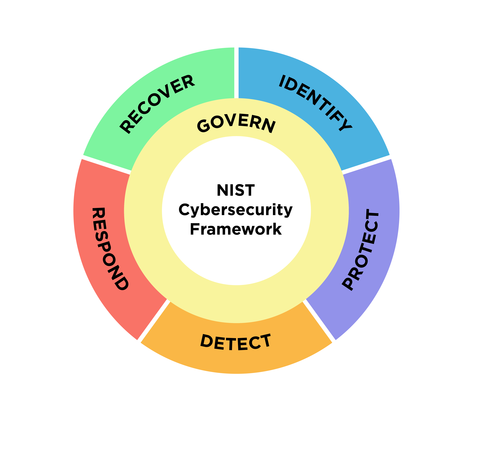
- Full alignment with NIST Cybersecurity Framework (CSF) 2.0
- Advanced threat detection and response
- Enterprise-grade compliance architecture
- Risk management and governance frameworks
- Protection for telecom networks, financial institutions, ISPs, and government entities
Framework-led
Structured methodology based on globally recognized standards
Risk-driven
Prioritization based on actual threat landscape and business impact
Business-aligned
Security initiatives directly support organizational objectives
Telecom-aware
Deep understanding of telecommunications infrastructure and challenges
Outcome-focused
Measurable results and continuous improvement
Our Framework
NIST CSF 2.0 National Institute of Standards andTechnologyCybersecurity Framework Version 2.0
Why NIST CSF 2.0?
Governance Alignment
Integrates cybersecurity into enterprise risk management and board oversight
Risk-Based Prioritization
Focus resources on highest-impact risks and critical assets
Maturity Measurement
Quantifiable assessment of cybersecurity posture and progress tracking
Regulatory Compatibility
Maps to global regulations including GDPR, NIS2, and industry standards
Board-Level Reporting
Clear, executive-friendly communication of cyber risk and program status
Cross-Domain Integration
Unified approach across IT, OT, Cloud, and Telecom environments
- GOVERN
Establish cybersecurity governance and risk management - IDENTIFY
Understand assets, risks, and vulnerabilities - PROTECT
Implement safeguards to reduce risk impact - DETECT
Identify cybersecurity events in real time - RESPOND
Take action when incidents occur - RESPOND
Take action when incidents occur
Implementation
Integrated Engagement Model
Four-Phase Structured Approach
Maturity Assessment
NIST CSF 2.0 scoring, Gap analysis, Risk heatmap
Strategic Roadmap
12-36 month plan, Budget prioritization, Quick wins identified
Implementation
Technology deployment, System integration, Security hardening
Operate & Optimize
Managed services, Continuous monitoring, Maturity reassessment
- Identity Protection
- Data Security
- SecOps
- Cloud Security
- Mobile Security
- Incident Response
- Governance & Compliance
Clear Visibility
Of cyber maturity and risk posture
Risk-Prioritized Investments
Focused on highest-impact areas
Reduced Attack Surface
Through comprehensive controls
Faster Detection & Response
Minimize incident impact
Regulatory Confidence
Meet compliance requirements
Improved Resilience
Bounce back from incidents
Executive-Level Oversight
Board visibility and governance alignment